Día Mundial De La Cuántica and the 2,048-bit alarm: why cryptography may be under pressure sooner than expected
Día Mundial De La Cuántica is usually framed as a celebration of scientific progress, but the latest research gives it a sharper edge: the same field inspiring optimism is also narrowing the timeline for classical encryption. In recent weeks, multiple research groups have argued that quantum machines may not need the immense scale once assumed to threaten today’s security systems. That matters because the discussion is no longer abstract. It now touches the practical future of Bitcoin, Ethereum and the broader cryptographic tools that protect digital information.
Why the latest findings matter right now
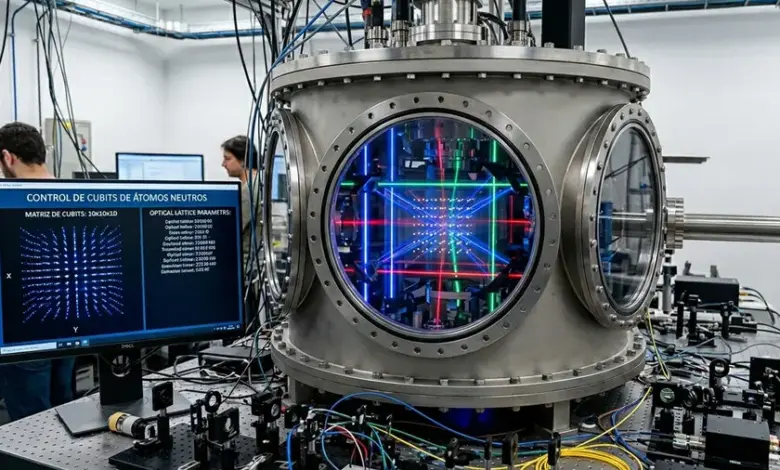
The immediate concern is not that quantum computers have already broken mainstream encryption at scale. The concern is that the threshold may be lower and closer than many assumed. A preliminary paper from researchers at the California Institute of Technology, the University of California, Berkeley and Oratomic examined neutral-atom quantum computers and estimated that Shor’s algorithm could be implemented on a machine with between 10, 000 and 20, 000 neutral-atom qubits. In that same work, the researchers outlined a theoretical design that could break Bitcoin encryption in a few days using 26, 000 neutral-atom qubits.
That estimate sits alongside another recent finding from Google’s quantum AI research group, which argued that elliptic-curve cryptography used by Bitcoin and Ethereum could be defeated with far fewer resources than earlier projections suggested. The group estimated that fewer than half a million physical qubits could decrypt the algorithms used by current cryptocurrencies in a matter of minutes. Taken together, these studies do not prove an immediate collapse, but they do compress the window in which classical systems can be treated as safely distant from quantum risk.
Día Mundial De La Cuántica and the shrinking margin for classical encryption
The deeper issue is not one research milestone alone, but the convergence of several independent signals. In May 2024, a team at Shanghai University led by Professor Wang Chao used a D-Wave quantum computer to successfully compromise SPN, a cryptographic algorithm used to encrypt information. That result matters because SPN is a foundational component in the logic that underpins the AES standard, which is widely used.
Then, in May 2025, Google researchers said that a 2, 048-bit RSA integer could be factored in less than a week with a quantum computer using fewer than one million qubits. RSA and elliptic-curve systems are not identical, and elliptic-curve cryptography is described in the context as more robust, efficient and harder to break than RSA. Even so, their mathematical foundations are similar enough that the warning carries weight. The pattern emerging from these studies is consistent: cryptographic assumptions built for classical computers are becoming less comfortable in a quantum setting.
This is why Día Mundial De La Cuántica is not only a science marker but a security marker. The field is moving from theoretical possibility toward narrowing engineering gaps, and each new estimate forces institutions to revisit how long current protections can be trusted as-is.
Expert perspectives and what the research is really saying
The clearest expert signal comes from the published findings themselves. The Caltech, Berkeley and Oratomic team framed neutral-atom machines as an experimental alternative to superconducting and trapped-ion quantum computers, but still concluded that the hardware needed to run Shor’s algorithm may be far closer than earlier assumptions suggested. Google’s researchers added another layer by arguing that the cost of breaking elliptic-curve cryptography could be substantially lower than expected.
Professor Wang Chao’s team at Shanghai University demonstrated that even a D-Wave system could be used to defeat SPN in practice. That does not mean every encryption layer is already vulnerable, but it does show that quantum advantage is no longer a purely hypothetical debate. The practical implication is clear: the migration away from classical cryptographic assumptions is becoming a planning issue, not a distant research topic.
Global impact: from cryptocurrency to broader data security
The most visible exposure lies in cryptocurrencies, because Bitcoin, Ethereum, Solana and similar systems rely on elliptic-curve cryptography. Yet the broader consequences extend well beyond digital assets. If research keeps converging on shorter timelines and lower qubit counts, then the security of confidential data, financial systems and encrypted communications will have to be reviewed with new urgency.
For now, the evidence points to vulnerability arriving before large-scale quantum hardware becomes commonplace. That distinction matters: institutions do not need to wait for full maturity before the risk becomes actionable. The latest studies suggest that the race is no longer simply about building quantum machines, but about whether security systems can adapt quickly enough to remain trustworthy while the hardware catches up.
As Día Mundial De La Cuántica highlights the promise of the field, it also raises the question that now hangs over every encrypted system: if classical cryptography is already being mapped for defeat, who has the faster timeline — quantum hardware, or the defenses meant to survive it?




