John Panicci and the Stolen Encrypted Key: 6 Questions Palm Beach’s Elections Office Must Now Answer
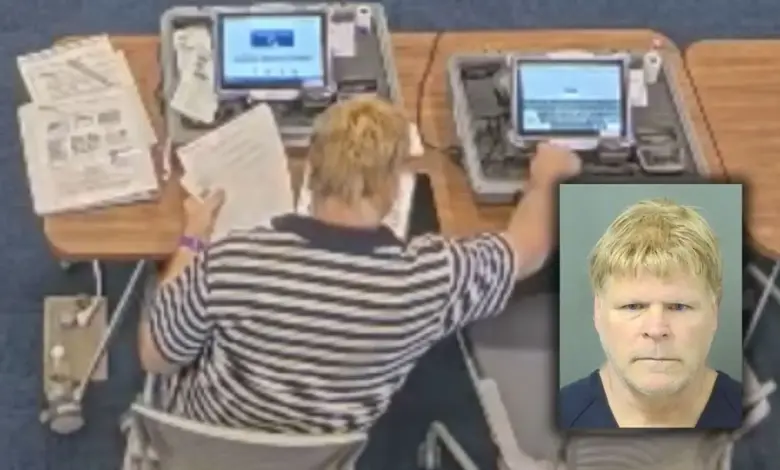
An election-security incident rarely begins inside a classroom-style training session, yet that is exactly what investigators say happened in Palm Beach County. John Panicci, a volunteer attending a training at the Palm Beach County Supervisor of Elections Office, was arrested after detectives alleged he took an encrypted access key from a voter registration terminal. Officials stressed the key was configured only for training databases, but they also flagged a harder reality: even “training-only” tools can become security liabilities when placed in the wrong hands.
What authorities say happened—and what remains unproven
Detectives with the Palm Beach County Sheriff’s Office responded to the Palm Beach County Supervisor of Elections Office at 4301 Cherry Road after sensitive computer equipment was reported stolen. Investigators later concluded the alleged theft occurred days earlier, on March 19, during a training session for volunteers assisting with an upcoming election.
In two separate accounts of the same case, authorities described the item as an encrypted access key taken from a voter registration terminal. The theft was reported to law enforcement on March 27, triggering the investigation. After detectives identified John Panicci as the suspect and established probable cause, they obtained an arrest warrant and a residential search warrant.
On March 28, detectives executed the search warrant at the suspect’s residence. Investigators said they recovered the stolen key and also found a significant or substantial amount of electronic and digital storage devices. John Panicci was taken into custody without incident, transported to the Palm Beach County Jail, and booked on charges that include theft and taking and damaging an electronic device. He made an initial court appearance Sunday morning and jail records show a $6, 000 bond.
Authorities have not said whether any voter data was compromised. That gap matters: it creates a clear line between what is currently alleged (theft of a key) and what has not been demonstrated publicly (any misuse of systems or exposure of data).
Why a “training-only” key can still become a high-stakes problem
The central tension in this case is the difference between configuration and capability. the encrypted access key was set up only for training databases. On its face, that appears to limit immediate damage. But investigators also articulated a concern that someone with technical expertise could reverse-engineer the encryption and use it in a live voter registration kiosk for malicious purposes.
This is where the John Panicci case moves beyond a basic theft allegation and into governance and risk management. If a training environment uses tools that resemble operational tools closely enough that they raise reverse-engineering concerns, then training is no longer just an administrative function—it becomes part of the attack surface. That does not prove wrongdoing beyond the alleged theft, but it does spotlight a key policy question: how should election offices structure volunteer training so that it is effective without exposing sensitive components that could be repurposed?
Equally important is chain-of-custody discipline. The allegations suggest a physical removal of an access key from a terminal during a session involving volunteers. The immediate editorial takeaway is not that the system is broken, but that procedures must anticipate insider-like risk in settings that are designed to be welcoming and educational.
Security, trust, and the investigations that follow
The case also illustrates how quickly operational concerns can spill into public confidence. Elections administrators depend on trust that access controls—both physical and digital—are strict even in non-election moments. Once an encrypted access key is described as “sensitive, ” the public naturally wants to know what “sensitive” means in practice: what that key could unlock, what it could not unlock, and what safeguards prevent misuse.
At this stage, the Palm Beach County Sheriff’s Office has emphasized that the investigation is ongoing. That framing is crucial because it signals that evidence collection and analysis may still be underway, including examination of the recovered electronic and digital storage devices. However, no public claim has been made that any of those devices were used to compromise voter information or election systems. Facts and analysis must be kept separate: the facts are the allegation of theft, the recovery of the key, and the ongoing investigation; the analysis is the broader risk question raised by the possibility of reverse-engineering.
For the Palm Beach County Supervisor of Elections Office, the incident is a stress test for training security design. Even if no voter data was compromised, the episode pressures administrators to demonstrate that sensitive equipment is controlled at every stage—especially when volunteers are present.
And for John Panicci, the legal process will determine what can be proven in court beyond the arrest and booking details now in the public record.
As the investigation continues, Palm Beach County faces a narrow but urgent question: if an encrypted access key can be removed during training, what additional controls will be put in place to ensure John Panicci becomes an exception rather than a precedent?





